What is ransomware, how serious is it and should I be worried?
A successful ransomware attack could easily see your business out of action. But what is ransomware? And what can you do to protect yourself?…
Currently considered to be one of the greatest online threats with the capacity to shut down entire networks, ransomware is something that we all need to be aware of.
What is ransomware?
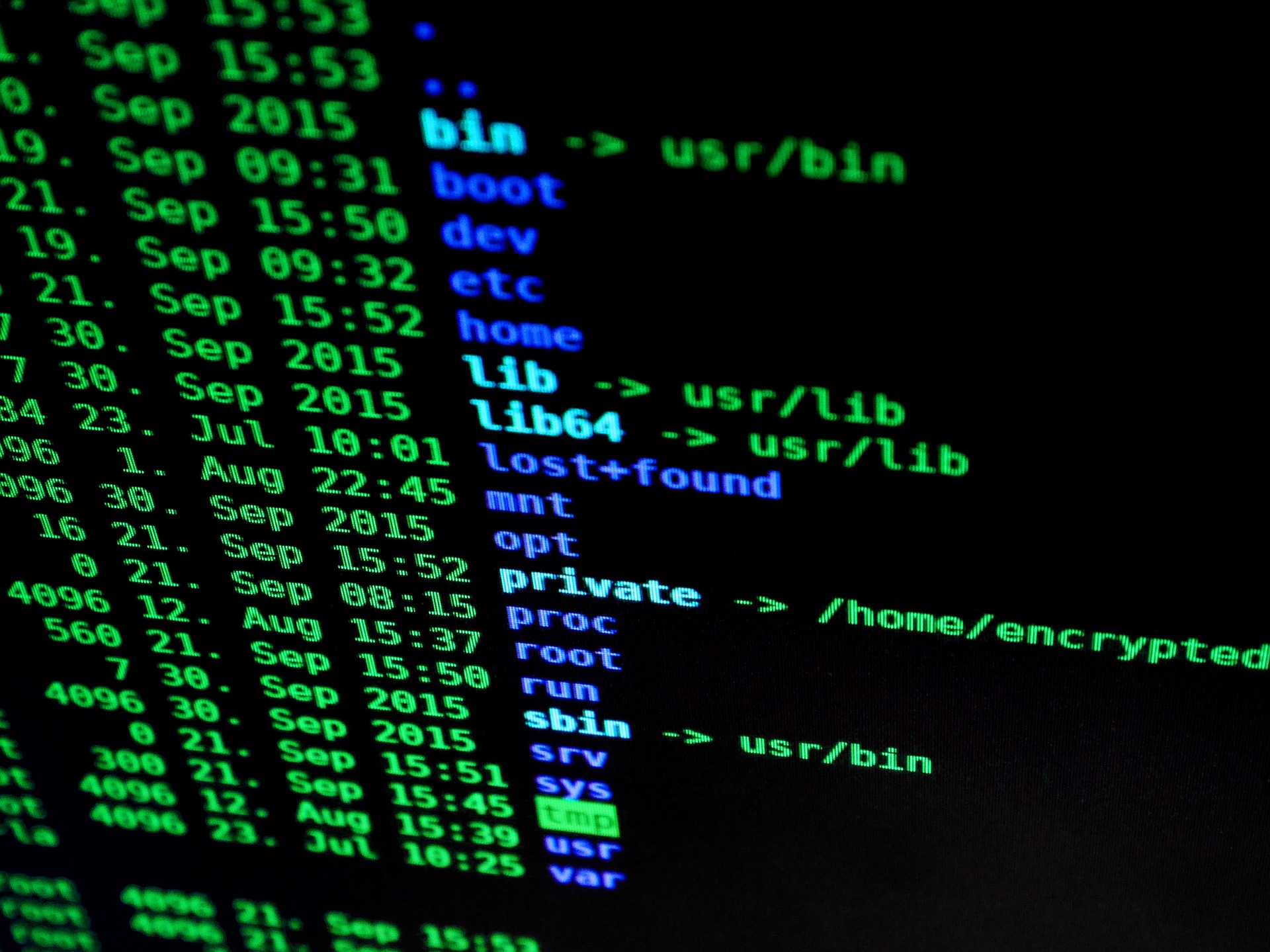
Ransomware is a malicious software (Malware) that infects a user’s computer by encrypting their documents and/or other files and blocking access to them. This information is then held for ‘ransom’ until the user pays a fee (often running into thousands of pounds) in exchange for a decryption code or key. It goes without saying, therefore, that the motivation for those carrying out ransomware attacks is almost always financial gain, with criminals often demanding their payment in a virtual currency such as Bitcoin in order to avoid revealing their true identities.
So, how does it work?
Criminals will disguise their intentions with what would appear to be an innocent link or attachment, often forming part of an email. The link will aim to draw users in as most ransomware is reliant upon interaction from a user in order to activate it. The moment the system or network has been compromised, specific files, or sometimes all of your files, will be taken control of by the malware and the user will no longer be able to access them.
The cyber attack victim will then be notified of the situation with the criminal outlining their demands and advising how the user can regain control of their files. Once paid, the user’s data is typically (but not always) restored. Cybercriminals are usually true to their word as this is in their best interest – if users were not getting their data back, then they are less likely to pay the ransom. That said, this is not always the case.
The origins of ransomware
It is reported that the first ever ransomware attack took place in 1989, targeting the healthcare industry. This particular instance was achieved by concealing malware on floppy disks along with an AIDS health questionnaire. The ransomware would then lie dormant on a user’s PC and would only be activated after the PC had booted-up 90 times. They would then demand the user to renew their license by sending $189 by mail. The encryption used was relatively simple to reverse, so it posed little threat to those who were computer savvy
Over three decades later, however, the healthcare industry remains a high priority for ransomware cybercriminals.
Ransomware – A timeline
Early ransomware attacks were reliant upon developers writing their own code with early forms being quite simple in their approach. For example, they would change the name of files using basic cryptography methods. These attempts were much smaller in scale than we are accustomed to today and would usually target general internet users.
After the initial ransomware attack in 1989, this type of cyber crime remained relatively uncommon until the mid-2000s. Attacks then began to utilise more sophisticated encryption algorithms. In 2011, a ransomware worm began to attack users which imitated the Windows Product Activation notice, making it difficult for users to tell the difference between genuine notifications and threats.
From April 2014 to March 2015, Kaspersky’s SecureList reports that the most prominent ransomware threats were CryptoWall, Cryakl, Scatter, Mor, CTB-Locker, TorrentLocker, Fury, Lortok, Aura, and Shade. The report states that: “Between them they were able to attack 101,568 users around the world, accounting for 77.48% of all users attacked with crypto-ransomware during the period.”
It wasn’t until the global panic caused by WannaCry in 2017, however, that malware entered the public consciousness. Today’s malware criminals can buy toolkits and/or ransomware as a service (RaaS) programs, which means those with minimal technical skills are able to download and deploy ransomware.
With new techniques emerging and increased availability, it has been reported that ransomware attacks more than doubled in 2019. McAfee Labs Threats Report recorded a 118% rise in attacks in the first quarter of 2019 alone. Malwarebytes Labs marked a monumental 365% increase in ransomware attacks from quarter 2 in 2018 and quarter 2 in 2019.
The biggest threats to the education sector between 2018 and 2019 have been malware, particularly adware and ransomware. Attackers are fully aware of schools having a limited budget, and often the budget is prioritised towards core curriculum activity, and not cyber security. ICT infrastructure in the education sector is often outdated and patches are no longer available for the legacy hardware they operate from.
Financial status is not always a factor in the attacker’s decision to target the education sector, they target them for the rich, valuable host of data that is far easier to access than private companies with more complex security systems.
What do I do next?
If you think your business is prone to threat from ransomware and you want to rest easy, knowing that your data is safe, there are a number of actions you can take…
- Backup your data – A future-proof method of ensuring your data is safe is to use secure cloud-based backup service such as Acronis back-up. Such a system should provide multi-layered security and high-level encryption services.
- Keep your software up to date – Cyber attackers target organisations using outdated software that can no longer be updated or ‘patched’. For instance, the WannaCry ransomware attack in May 2017 targeted organisations that used computers running older versions of the Microsoft Windows operating system; versions that had not installed (or were unable to install) Microsoft’s security update from April 2017. In other words, those running unsupported versions of Windows – Windows XP and Windows Server 2003.
- Prioritise your investments in cyber security – With attacks on the rise, cyber security for your businesses should be at the forefront of your mind. Protect your organisation before it’s too late.
- Educate your teams – Alerting your teams to the common methods of malware and ensuring they are aware of the threats can only boost your chances of avoiding an attack. Encourage your employees on the need to use strong passwords and advise them to be one step ahead of cyber attackers.
- Be careful! – It may sound like common sense but, when it comes to cyber security, the phrase ‘better to be safe than sorry’ has never been more relevant. Never click any links or open any attachments within any emails that you’re not expecting. If you’re not expecting a parcel from that particular courier, don’t open an email or click a link purporting to be from them. Remember, ransomware files can look exactly like a Word, Excel, PDF or any other kind of file. It’s essential, therefore, that you take the utmost care when opening attachments. When in doubt… don’t open it!







